Enterprise-Grade Signatures. Startup-Friendly Pricing.
Join 500+ teams automating document logistics with ephemeral security, 60% average cost savings, and 100% data sovereignty.

Scale Document Logistics
Enterprise-grade visibility

Immutable Provenance
SHA-256 Chain Integrity
Engineered to outperform.
| Capability Framework | IUSign | Legacy Vendor D | Legacy Vendor S |
|---|---|---|---|
| Bulk Send Pipeline | Built-in / Unlimited | No | Limited |
| Domain White-labeling | Standard / Native | Enterprise Only | No |
| API Ecosystem | Developer-First / Full | Restricted / Tiered | Restricted |
| Envelope Surcharge | Non-existent | Usage-based Fees | Usage-based Fees |
| GCP KMS Key Control | Included / Native | Unavailable | Unavailable |
| Cryptographic Provenance | SHA-256 Chaining | None | None |
Current Feature Matrix Verification: April 2026
Core Ecosystem
Full Stack. Zero Bloat.
Visual Document Preparation
Drag-and-drop signature, text, date, and checkbox fields directly onto your PDF. Upload PDF or DOCX — automatic conversion via LibreOffice.
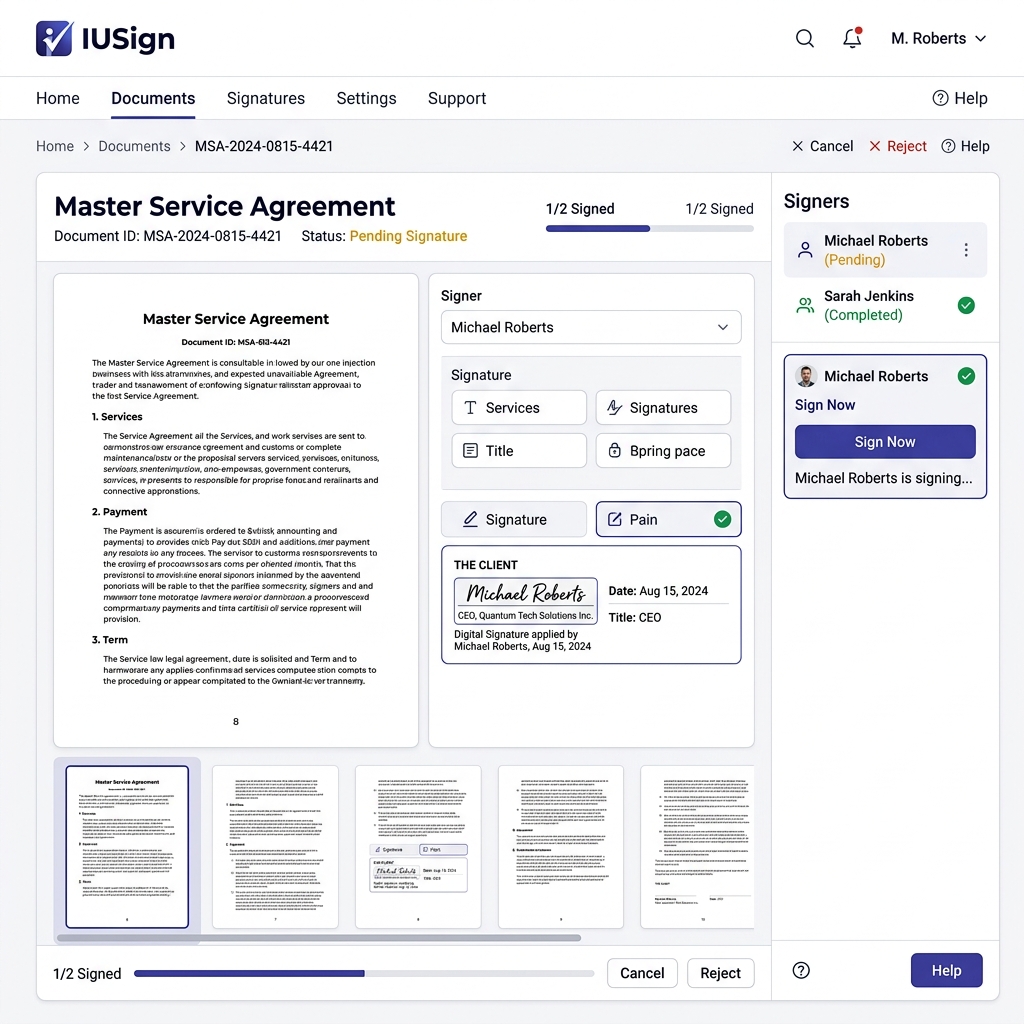
Sequential Multi-Party Signing
Define signing order: Person 1 → Person 2 → Person 3. Each signer receives the document only when it's their turn.
Immutable Audit Trail
Database-level triggers physically prevent deletion or modification of audit logs. SHA-256 hash chain per event.
Change Request & Revision Workflow
Signers click anywhere on the PDF to place comment pins. You resolve, upload a revised document, and re-send — all version-tracked.
Full White-Label Capability
Custom logo, brand colors, organization name, custom email from address, custom domain with DNS verification. Per-tenant usage limits enforced.
Smart Email Delivery
Redis-backed queue with exponential backoff retry. 4 Jinja2 email templates with custom composer and variable substitution.
Stuck Document Detection
Automatically detects documents inactive for 7+ days. Status filters, manual reminders, and blocker identification.
Developer API & SDK
39 documented endpoints. Postman collection, Python SDK, Swagger UI, HMAC-signed webhooks with retry, idempotency support.
Infrastructure-Level Trust
AES-256-GCM GCP KMS Envelopes
Your document is encrypted with a unique data encryption key (DEK) before it ever touches disk. The DEK itself is wrapped with a master key controlled in your GCP KMS instance.
Deploy Control KeySHA-256 Hash Chain Integrity
Every signature event — envelope created, document viewed, signature applied — is cryptographically chained. If a single record is altered, the entire chain triggers a violation.
Validate IntegrityEphemeral Zero-Persistence Flow
Raw document content exists only in temporary memory buffers during processing. We physically collect garbage (GC) and overwrite memory sectors after encryption.
Simulate BreachImmutable PDF Flattening
Signatures aren't just invisible overlays; they are physically burned into the document's structure at 300 DPI, creating a permanent, flattened forensic record.
Verify ProvenanceUniversal Evidence Package
Export a self-contained, court-ready JSON bundle containing all metadata, signer IP logs, intent capture, and the full hash chain provenance.
Download BundleHMAC-Signed Idempotent Pipelines
Webhooks aren't just POST requests. They are HMAC-signed for security and support idempotent retry logic to ensure your backend stays in perfect sync.
Test EndpointTake control of your
document logistics.
Self-hosted ephemeral security, immutable audit trails, and 100% data sovereignty starts here.